
| Employees watch an electronic board to monitor possible ransomware cyberattacks at the Korea Internet and Security Agency in Seoul, Monday. / Yonhap |

- AhnLab ASEC has gathered Excel files that leak user info using malicious macro. The Excel file prompts the user to run macro, and when macro is run, it re-runs the Excel document that contains a court decision stating that the user ‘must pay a fine for abetting a breach on the Act On Door-To-Door Sales, etc. To make it difficult for the users to realize that their PC is infected.
- The Evolution of Magniber Ransomware. This analysis report will examine the recent malicious activities of Magniber ransomware from changes in exploited vulnerability to shellcode. PDF Downloads; Sour Lemon Duck: PowerShell Malware Exploiting SMB Vulnerability.
Gov't issues nationwide caution against WannaCryptor
By Yoon Sung-won
The worldwide spread of 'WannaCryptor' ransomware is raising a warning flag on cybersecurity in Korea even though it has not yet inflicted heavy damage here.
The Korea Internet & Security Agency (KISA) said Monday it has received nine official reports of the attack. CJ CGV, whose ad servers were affected by the malware, has not registered a report. No public organization has reported any damage yet.
The ransomware, which is also known as 'WannaCry,' has been attacking servers of enterprises and public organizations worldwide, especially in Europe, since last Friday. According to Europol, it has affected about 200,000 computers in more than 150 countries.
The ransomware encrypts a victim's data and demands cyber payments ranging from $300 to $20,000. The attackers threaten to delete the encrypted files if they don't receive the ransom in seven days.
Consequently, concerns have escalated that servers of many Korean companies and government agencies could be exposed to the attack when they start business this week.
On Sunday, the Ministry of Science, ICT and Future Planning released a caution on the national cyber threat level. KISA also introduced a dedicated information website to the public. But this website crashed as of 9 a.m. Monday amid heavy traffic. The agency said it has received over 2,900 calls about the ransomware.
Cheong Wa Dae also called for nationwide caution on the issue.
'The damage inflicted by the ransomware, which abuses loopholes in Microsoft's Windows operating system, is spreading worldwide,' the presidential office said in a statement, Monday. 'We need thorough contingency plans to prevent damage.'
Cheong Wa Dae's chief press secretary Yoon Young-chan said, 'The National Security Office is taking actions to prevent the spread of damage.' He also advised people to turn their computers on and off while disconnected from the internet, deactivate server message block protocols and update antivirus programs.
Besides the government and public agencies, cybersecurity service providers and experts in the private sector said people should stay alert because there can be more diverse forms of ransomware attacks.
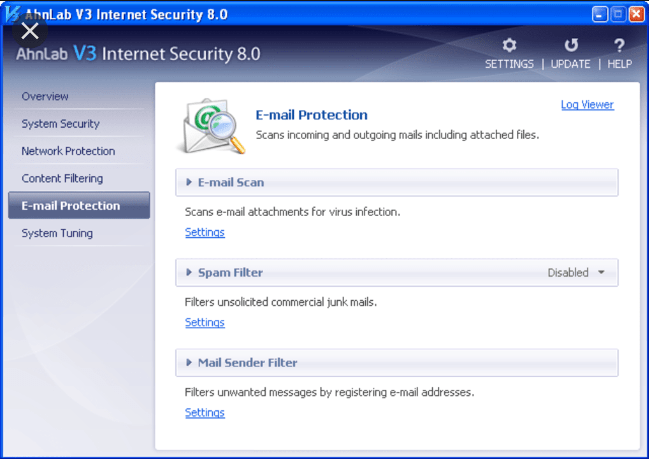
AhnLab, provider of the antivirus program V3 series, advised its users to turn on real-time monitoring and install updates. It also said Windows users should keep the operating system's security features up to date.
'Korea is expected to have less damage compared to other countries thanks to quick responses from public agencies and security companies,' an AhnLab official said. 'But there can still be more new types of cyberattacks.'
ESTsecurity, which provides the antivirus program Alyac series, said its program detected more than 3,000 ransomware attacks on Sunday.
Symantec Korea pointed out the WannaCry ransomware is especially contagious because it is capable of spreading within an intranet on its own. The company also stressed the importance of timely security updates of Windows to prevent further damage.
'Users should keep security patches and antivirus software up to date because there can be more cyberattacks with ransomware and viruses,' Symantec Korea CTO Yoon Kwang-taek said. 'In particular, the number of ransomware attacks through email is on the rise. Users should delete suspicious e-mails and back up important files in advance.'
Ahnlab Ransomware
AhnLab’s V3 products detect STOP ransomware under the following alias: - Malware/Win32.Ransom - Malware/Win32.Generic - Trojan/Win32.Generic - Win-Trojan/Gandcrab10.Exp. Chat feature was not able to connect when security researchers at AhnLab analyzed the relevant ransomware. Elaborate designs Some ransomware suspiciously display irregular designs, whereas many ransomware and variants poorly. AhnLab – Leader in Cyber Threat Analysis and Response!! Ransomware is continuing to evolve. Now, ransomware is largely changing from file encryption and money demands based programs to stealing informatio.